www.census.abs.gov.au SSL/TLS Security Test on 29 July 2016:
This is one example:
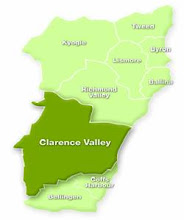
This blog is open to any who wish to comment on Australian society, the state of the environment or political shenanigans at Federal, State and Local Government level.

Hi! My name is Boy. I'm a male bi-coloured tabby cat. Ever since I discovered that Malcolm Turnbull's dogs were allowed to blog, I have been pestering Clarencegirl to allow me a small space on North Coast Voices.
A false flag musing: I have noticed one particular voice on Facebook which is Pollyanna-positive on the subject of the Port of Yamba becoming a designated cruise ship destination. What this gentleman doesn’t disclose is that, as a principal of Middle Star Pty Ltd, he could be thought to have a potential pecuniary interest due to the fact that this corporation (which has had an office in Grafton since 2012) provides consultancy services and tourism business development services.
A religion & local government musing: On 11 October 2017 Clarence Valley Council has the Church of Jesus Christ Development Fund Inc in Sutherland Local Court No. 6 for a small claims hearing. It would appear that there may be a little issue in rendering unto Caesar. On 19 September 2017 an ordained minister of a religion (which was named by the Royal Commission into Institutional Responses to Child Sexual Abuse in relation to 40 instances of historical child sexual abuse on the NSW North Coast) read the Opening Prayer at Council’s ordinary monthly meeting. Earlier in the year an ordained minister (from a church network alleged to have supported an overseas orphanage closed because of child abuse claims in 2013) read the Opening Prayer and an ordained minister (belonging to yet another church network accused of ignoring child sexual abuse in the US and racism in South Africa) read the Opening Prayer at yet another ordinary monthly meeting. Nice one councillors - you are covering yourselves with glory!
An investigative musing: Newcastle Herald, 12 August 2017: The state’s corruption watchdog has been asked to investigate the finances of the Awabakal Aboriginal Local Land Council, less than 12 months after the troubled organisation was placed into administration by the state government. The Newcastle Herald understands accounting firm PKF Lawler made the decision to refer the land council to the Independent Commission Against Corruption after discovering a number of irregularities during an audit of its financial statements. The results of the audit were recently presented to a meeting of Awabakal members. Administrator Terry Lawler did not respond when contacted by the Herald and a PKF Lawler spokesperson said it was unable to comment on the matter. Given the intricate web of company relationships that existed with at least one former board member it is not outside the realms of possibility that, if ICAC accepts this referral, then United Land Councils Limited (registered New Zealand) and United First Peoples Syndications Pty Ltd(registered Australia) might be interviewed. North Coast Voices readers will remember that on 15 August 2015 representatives of these two companied gave evidence before NSW Legislative Council General Purpose Standing Committee No. 6 INQUIRY INTO CROWN LAND. This evidence included advocating for a Yamba mega port.
A Nationals musing: Word around the traps is that NSW Nats MP for Clarence Chris Gulaptis has been talking up the notion of cruise ships visiting the Clarence River estuary. Fair dinkum! That man can be guaranteed to run with any bad idea put to him. I'm sure one or more cruise ships moored in the main navigation channel on a regular basis for one, two or three days is something other regular river users will really welcome. *pause for appreciation of irony* The draft of the smallest of the smaller cruise vessels is 3 metres and it would only stay safely afloat in that channel. Even the Yamba-Iluka ferry has been known to get momentarily stuck in silt/sand from time to time in Yamba Bay and even a very small cruise ship wouldn't be able to safely enter and exit Iluka Bay. You can bet your bottom dollar operators of cruise lines would soon be calling for dredging at the approach to the river mouth - and you know how well that goes down with the local residents.
A local councils musing: Which Northern Rivers council is on a low-key NSW Office of Local Government watch list courtesy of feet dragging by a past general manager?
A serial pest musing: I'm sure the Clarence Valley was thrilled to find that a well-known fantasist is active once again in the wee small hours of the morning treading a well-worn path of accusations involving police, local business owners and others.
An investigative musing: Which NSW North Coast council is batting to have the longest running code of conduct complaint investigation on record?
A fun fact musing: An estimated 24,000 whales migrated along the NSW coastline in 2016 according to the NSW National Parks and Wildlife Service and the migration period is getting longer.
A which bank? musing: Despite a net profit last year of $9,227 million the Commonwealth Bank still insists on paying below Centrelink deeming rates interest on money held in Pensioner Security Accounts. One local wag says he’s waiting for the first bill from the bank charging him for the privilege of keeping his pension dollars at that bank.
A Daily Examiner musing: Just when you thought this newspaper could sink no lower under News Corp management, it continues to give column space to Andrew Bolt.
A thought to ponder musing: In case of bushfire or flood - do you have an emergency evacuation plan for the family pet?
An adoption musing: Every week on the NSW North Coast a number of cats and dogs find themselves without a home. If you want to do your bit and give one bundle of joy a new family, contact Happy Paws on 0419 404 766 or your local council pound.
No comments:
Post a Comment